Securing Our Future: A Comprehensive Guide to IT Security Challenges and Solutions
In a world increasingly interconnected through technology, IT security has become a critical priority for individuals and organizations alike. Today, it encompasses protecting data, systems, and networks from cyber threats, making it a cornerstone of modern life. This article delves into the multifaceted nature of IT security, exploring key challenges and the innovative solutions driving the industry forward.
The Importance of IT Security in Today’s World
IT security is no longer a reactive measure; it is a proactive necessity. From safeguarding personal data to protecting critical infrastructure, the scope of IT security has expanded dramatically. The rapid pace of technological advancement has given rise to new vulnerabilities, making robust IT security frameworks imperative for:
- Individuals: Protecting personal data, financial information, and privacy.
- Businesses: Ensuring operational continuity, intellectual property safety, and customer trust.
- Governments: Securing critical infrastructure, national security, and public services.
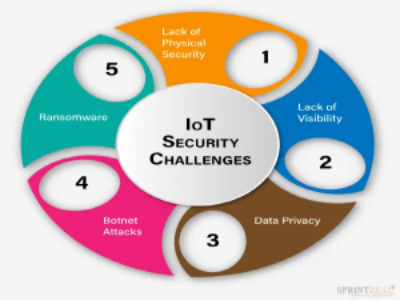
Emerging Threats in the IT Security Landscape
The modern IT security landscape is rife with challenges. Understanding these threats is the first step toward effective mitigation:
- Cybersecurity Threats:
- Ransomware Attacks: Disruptive and costly for businesses and individuals.
- Phishing Scams: Manipulative techniques targeting unsuspecting users.
- Data Breaches: Exposing sensitive information to malicious actors.
- Advanced Persistent Threats (APTs):
- Stealthy, long-term campaigns targeting high-value information.
- Insider Threats:
- Security risks from within organizations due to negligence or malicious intent.
- Supply Chain Attacks:
- Compromising third-party vendors to infiltrate primary targets.
Cutting-Edge Solutions in IT Security
To counter these threats, the IT security industry has embraced a range of innovative solutions:
- Zero Trust Architecture:
- Verifying every user and device before granting access.
- Minimizing attack surfaces and reducing insider threats.
- AI and Machine Learning:
- Predicting and mitigating cyber threats through advanced analytics.
- Automating threat detection and response.
- Encryption and Data Protection:
- Employing end-to-end encryption for secure communication and data storage.
- Utilizing secure backup solutions to recover from data loss.
- Identity and Access Management (IAM):
- Strengthening authentication processes with multi-factor authentication (MFA).
- Implementing role-based access control (RBAC) to limit unnecessary access.
Best Practices for IT Security
IT security is a shared responsibility. Here are actionable steps for individuals and organizations:
- For Individuals:
- Use strong, unique passwords and enable MFA.
- Avoid clicking on suspicious links or downloading unverified files.
- Secure personal devices with antivirus software and regular updates.
- For Organizations:
- Conduct regular security audits and vulnerability assessments.
- Train employees on recognizing and responding to cyber threats.
- Implement comprehensive endpoint security solutions.
The Role of Governments and Policies
Governments play a crucial role in fostering a secure digital environment. Through legislation and initiatives, they:
- Establish cybersecurity frameworks and data protection laws.
- Promote public awareness campaigns on IT security practices.
- Foster international collaborations to address global cybersecurity challenges.
The Future of IT Security
As technology evolves, so too will IT security challenges and solutions. Key trends to watch include:
- AI and Automation:
- Streamlining threat detection and response.
- Enhancing predictive capabilities to prevent incidents before they occur.
- Quantum Computing:
- Offering new possibilities for encryption and decryption.
- Posing potential risks if misused by malicious actors.
- Ethical Considerations:
- Balancing security measures with privacy rights.
- Ensuring inclusivity and fairness in IT security technologies.
Conclusion
IT security is an ever-evolving field, critical to safeguarding our digital world. By staying informed, adopting innovative technologies, and fostering collaboration between individuals, organizations, and governments, we can build a safer, more secure future. As threats grow more sophisticated, so too must our resolve to address them with vigilance and ingenuity.
(This "Security Blogs" Published in February 2025 Edition)





.png)







